News of the Heartbleed OpenSSL vulnerability has caused a widespread security fever. A lot of major websites were affected by the bug and many took quick steps to fix the problem. One of the main issues with Heartbleed is that changing your password won’t protect you until the website patches the bug.
While the focus of Heartbleed has been on website security, Android is also affected. ArsTechnica found that users with Android 4.1.1 and “some versions of Android 4.2.2 that have been customized by the carriers or hardware manufacturers” may also have the flaw.
There are various ways that attackers can attempt to use the exploit on Android, one of which is using a booby-trapped website that will attempt to load unauthorized commands. This allows hackers to sniff out sensitive data from legitimate sites from a device’s memory.
Lookout Mobile Security released Heartbleed Detector, an app that scans your device to see if it is vulnerable to the bug. After it checks which version of OpenSSL your device is running, it scans if the specific vulnerability is present.
Testing different devices
I did a scan of various Android devices in the office as old as a HTC Thunderbolt running Android 2.3.4. Unfortunately, I couldn’t get an update of Google Play Services to install and update the device, so I can’t say for certain if this version of Android is vulnerable. But if you’re still using a device running older versions of Android, you may want to think about upgrading for increased security.
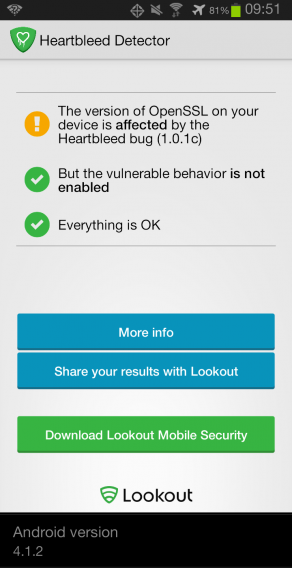
After leaving Verizon Wireless, I haven’t been able to upgrade the firmware of the Samsung Galaxy S3 so it’s been stuck on Android 4.1.2. Since it’s now used solely as a MP3 player, I don’t access any accounts or data online. In this particular case, any patch that is released will likely come from Verizon Wireless or Samsung and pushed to the device. If you’re using the device on a wireless carrier, you should see an update notification when the fix is released.
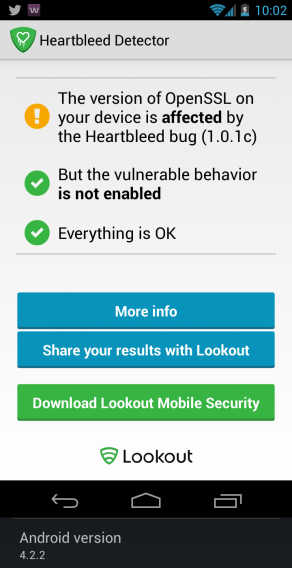
The Galaxy Nexus is no longer supported by Google, so it’s stuck at Android 4.2.2 in its stock form. It is possible to add a custom ROM to get more features, but since it serves to test apps with this version of Android, it’s good to see that it’s not vulnerable.
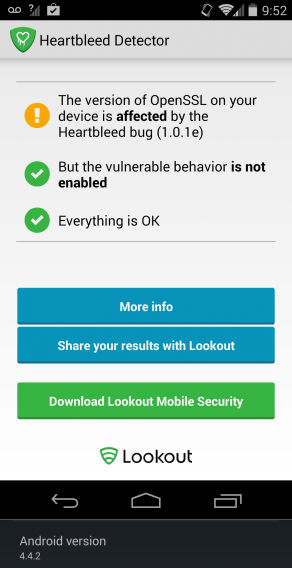
The last device we tested was the Nexus 5, Google’s latest flagship phone. Unfortunately like the other devices, it’s affected by the bug but on the positive side, the vulnerability isn’t enabled on the device. This doesn’t mean the device is 100% secure, but you are less likely to have problems directly related to Heartbleed. If you own the Nexus 5, Google will be pushing the patch directly to the device when it’s ready.
Don’t get tricked
Note that Heartbleed Detector doesn’t fix any vulnerabilities with Heartbleed. These vulnerabilities have to be patched by Google and the device manufacturer . If you are using a wireless carrier’s branded device, you should contact them to find out how they will patch Heartbleed.
Heartbleed Detector also won’t list any apps that might be affected so check with each developer. It’s a good idea to keep all your apps updated by going to the Play Store and tapping on “My Apps.” You will find any apps that need updating here.
As of now, Lookout hasn’t seen anyone attempting to exploit the bug on mobile devices, but be aware if apps or websites ask for too many permissions. Pay attention to URLs you visit on your site and don’t enter personal information on sites you don’t trust.
For more information, check out Heartbleed: the bug that left the internet vulnerable.


